...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
...
| Div | ||
|---|---|---|
| ||
| /wiki/spaces/E2D/pages/29982926 / Single Sign-On and MFA / Configuring SSO Connections / Service Provider Connections / Current: Setting up SSO with Office 365 |
The EmpowerID SSO framework allows you to federate EmpowerID with Office 365 without requiring you to set up ADFS or DirSync. In this scenario, the EmpowerID STS replaces ADFS, making EmpowerID the identity provider for your organization's Office 365 services.
| Note |
|---|
If Windows Azure AD Module for Windows PowerShell and MSOL Sign-In Assistant are already installed on your EmpowerID server, you must remove them before installing the newer versions. |
...
| title | Prerequisites |
|---|
You must have a licensed corporate Office 365 account and connect it to EmpowerID.
You must install the following modules in this order on the machine on which you configure the SSO Connection.
...
This topic describes how to federate EmpowerID with Office 365.
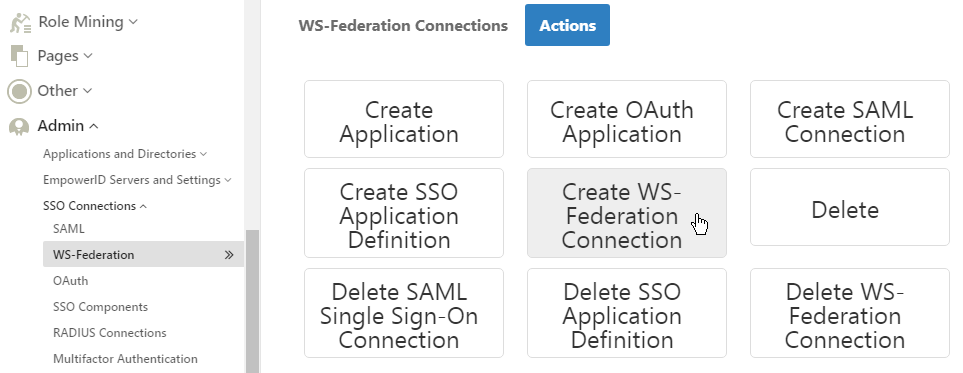
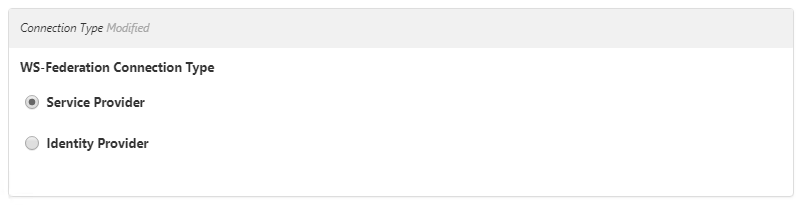
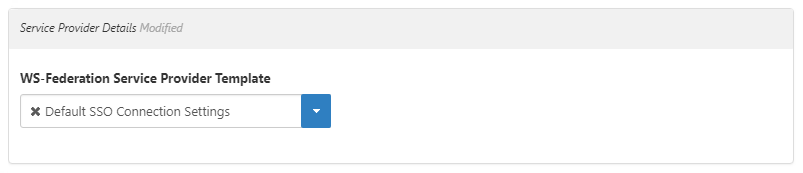
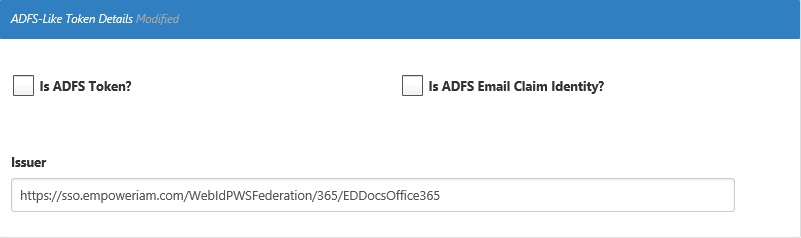
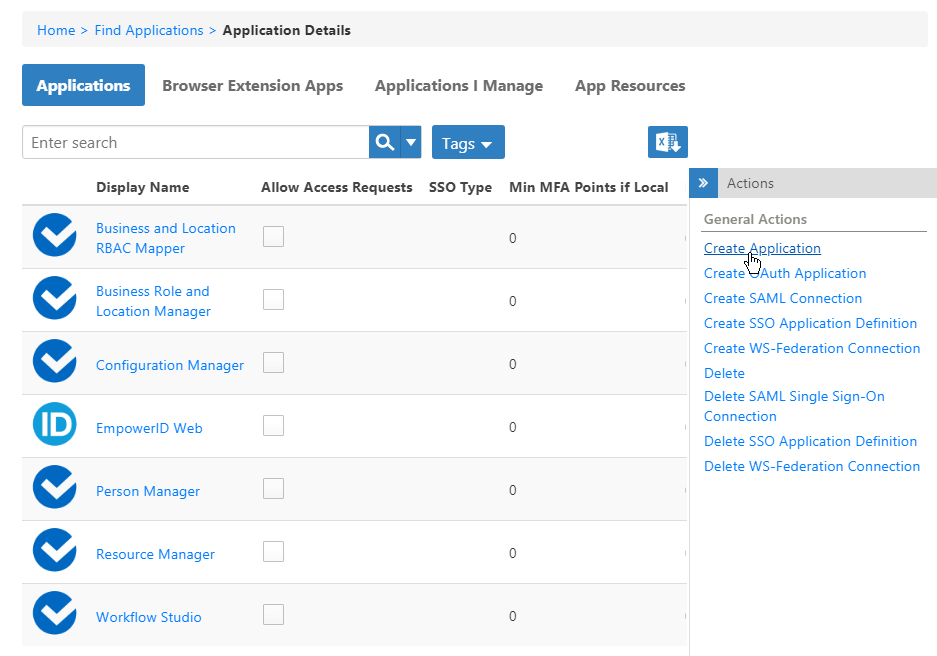
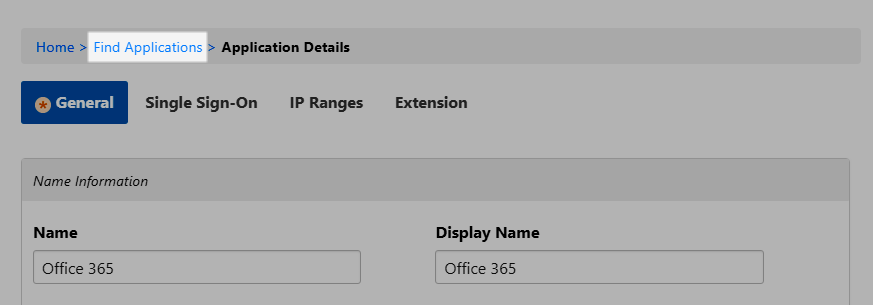
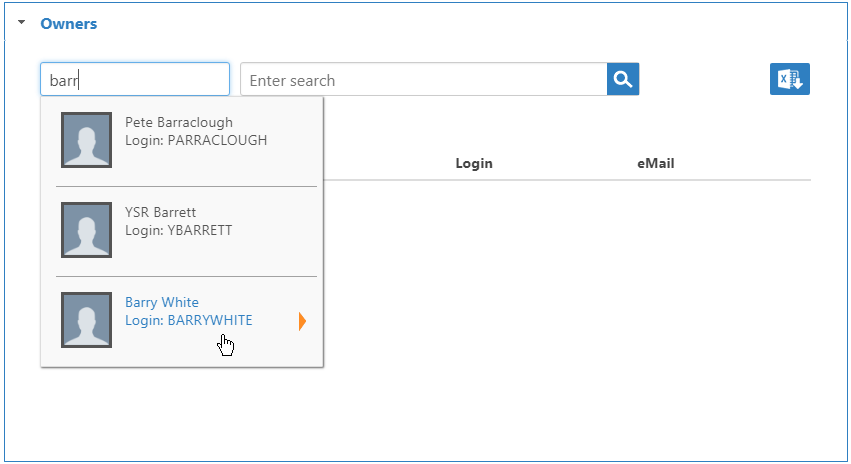
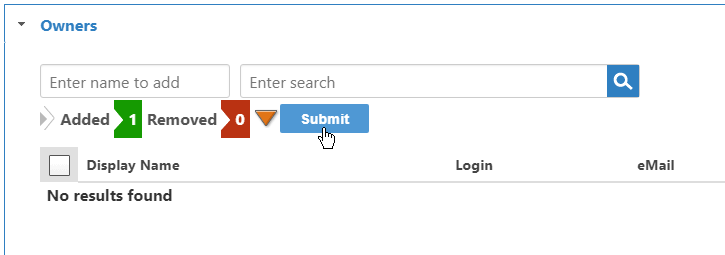
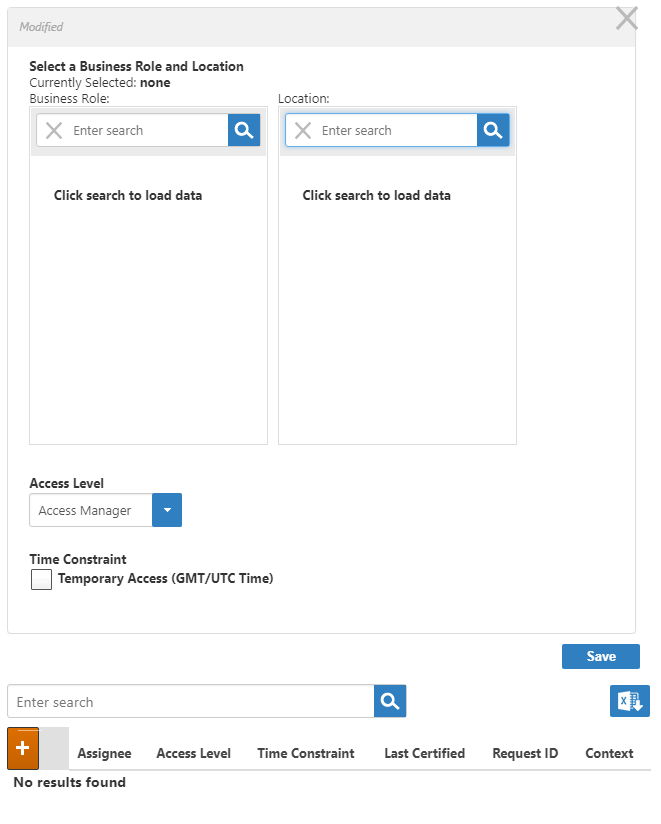
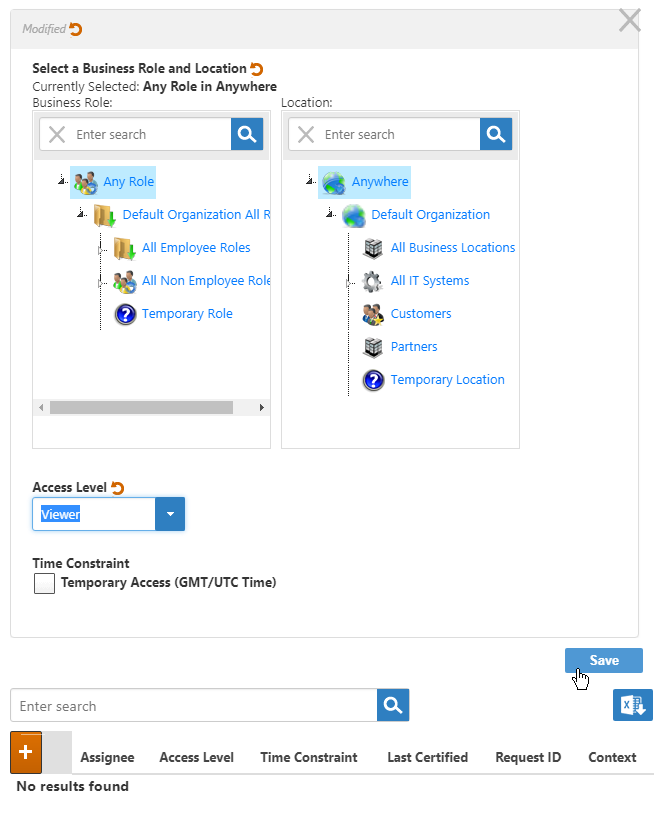
To create an SSO application for Office 365
...
Next, set the Public DNS for your server to match the domain name you are federating in Office 365 as described below.If the two already match you can skip ahead to Configuring a Trusted Endpoint for the SSL certificate used in your EmpowerID deployment.
To configure an EmpowerID server with a DNS Alias
This is an optional step that is only required when the DNS for your server and the domain name you registered in Office 365 are not the same. These values must match for SSL endpoints to function correctly. By setting a DNS, you are directing the EmpowerID services to ignore the machine's FQDN and use the Public DNS in its place.
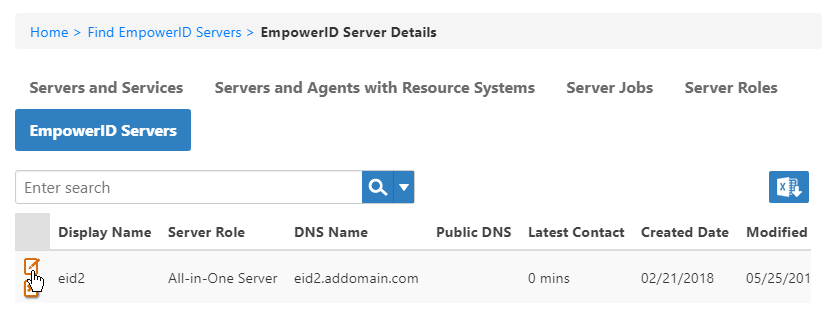
- From the Navigation Sidebar of the EmpowerID Web interface, navigate to the EmpowerID Server Details page by expanding Admin > EmpowerID Servers and Settings and clicking EmpowerID Servers.
- From the EmpowerID Server Details page, click the EmpowerID Servers tab and search for the server whose role you want to set.
- Click the Edit button for that server.
- In the dialog that appears, enter the DNS Alias in the PublicDns field and then click Save.
- Restart the EmpowerID services on that server.
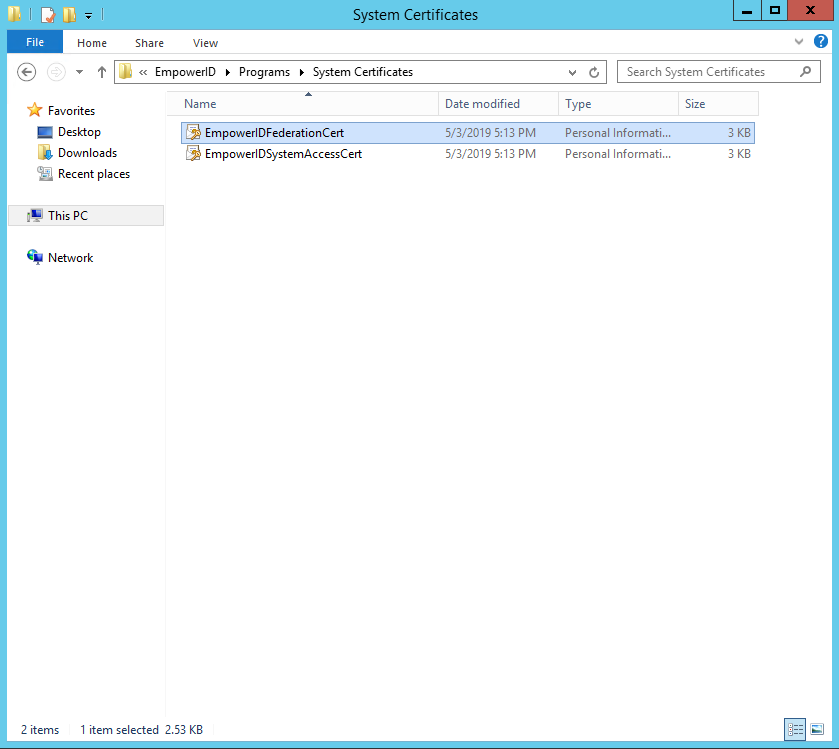
To export the EmpowerID Certificate in base64-encoding format
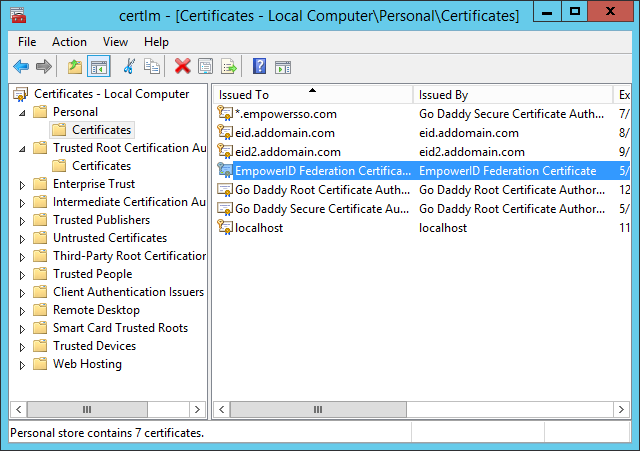
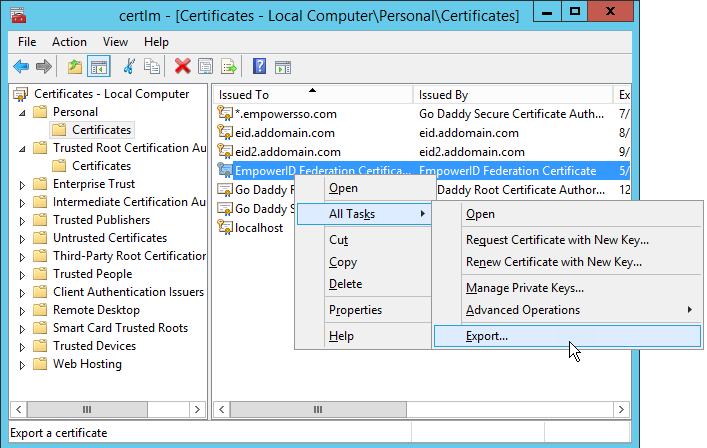
- From the server with your certificate, open the console root with the certificates snap-in (usually named Console 1). If you do not have the console configured with the certificates snap-in, open MMC and add the snap-in.
- From Console 1, expand the Certificates (Local Computer) > Personal nodes and then click Certificates.
- From the Personal certificates store, right-click the certificate you are using in your EmpowerID deployment and select All Tasks > Export from the context menu.
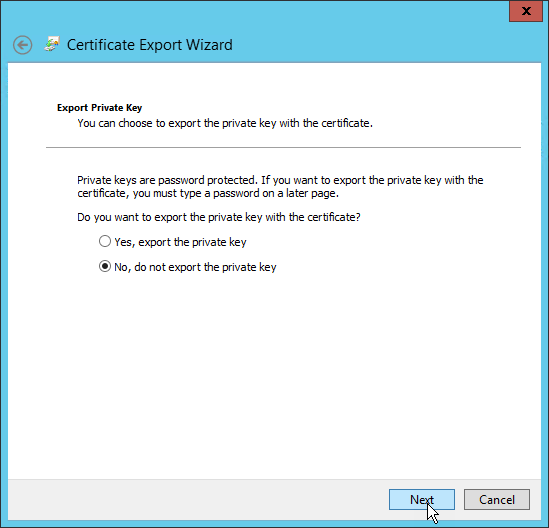
- In the Certificate Export Wizard that appears, click Next.
- Select No, do not export the private key and click Next.
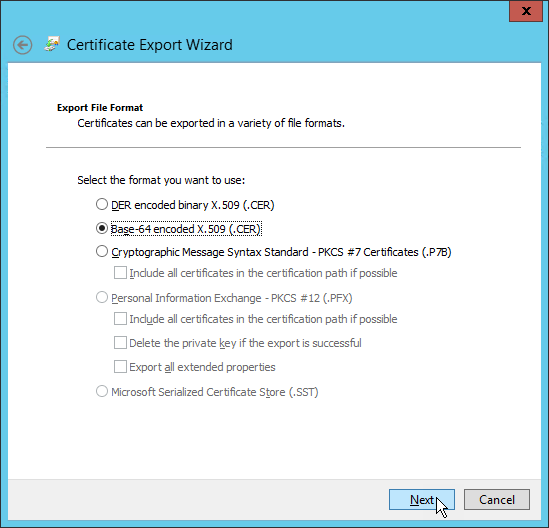
- Select Base-64 encoded X.509 (.CER) and click Next.
- Select an export location, naming the exported certificate accordingly and click Next.
- Click Finish to complete the export.
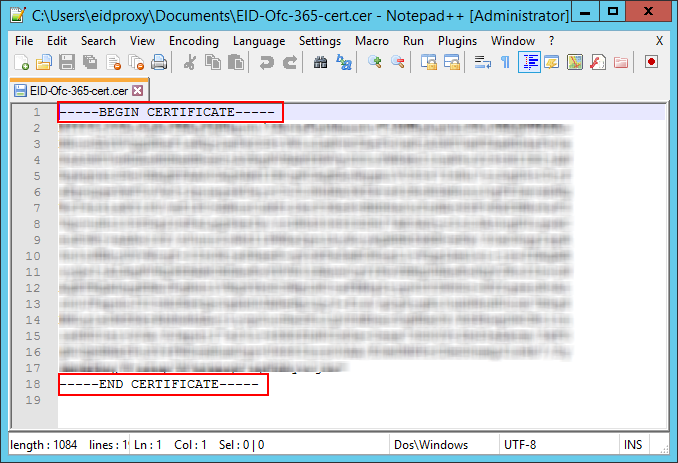
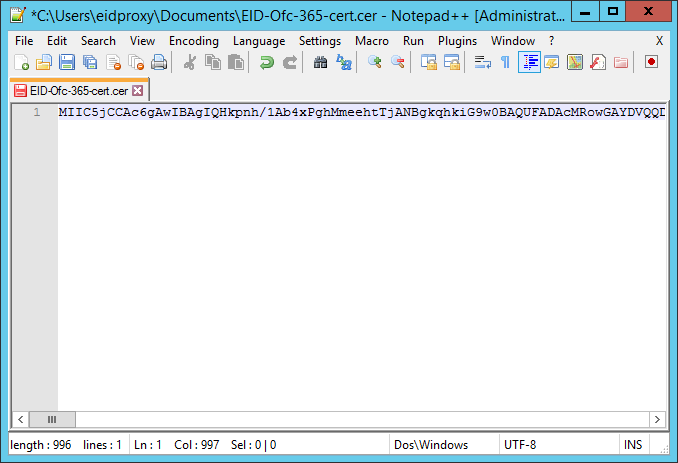
- Open the exported certificate in a text editor and remove the first and last lines (----BEGIN CERTIFICATE----and ----END CERTIFICATE----).
- Remove all spaces and line breaks so that the certificate appears on one line.
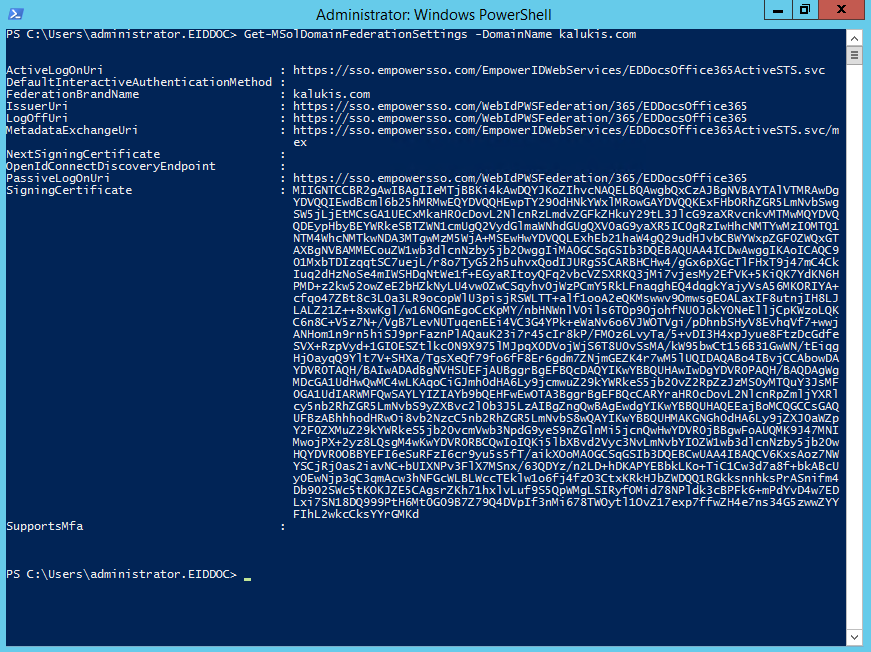
Next, establish trust between Office 365 and EmpowerID as described below.
To establish trust between Office 365 and EmpowerID
...
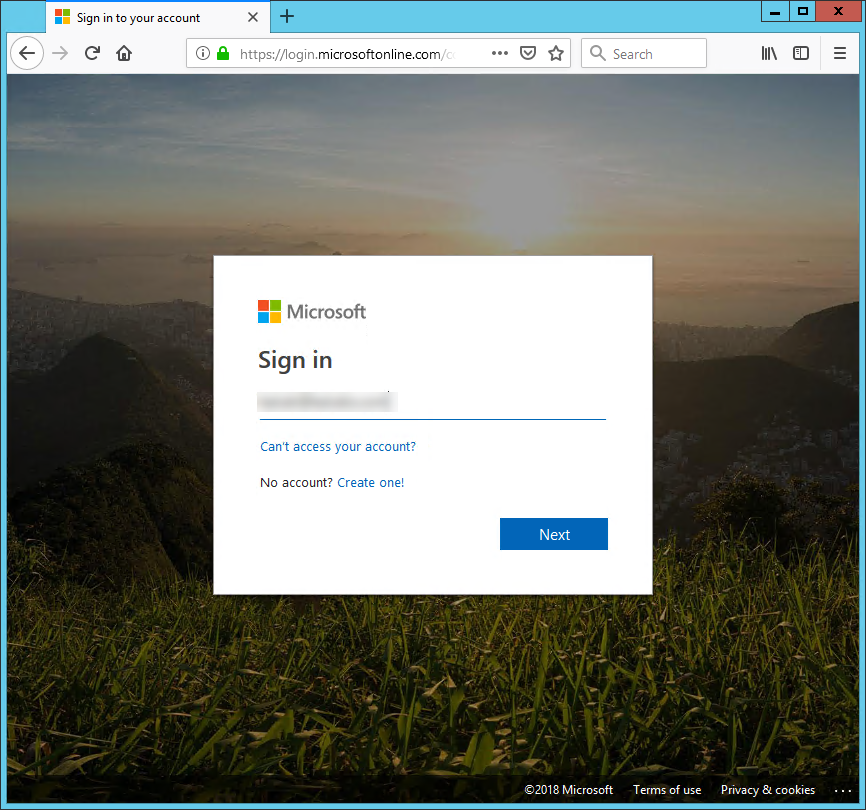
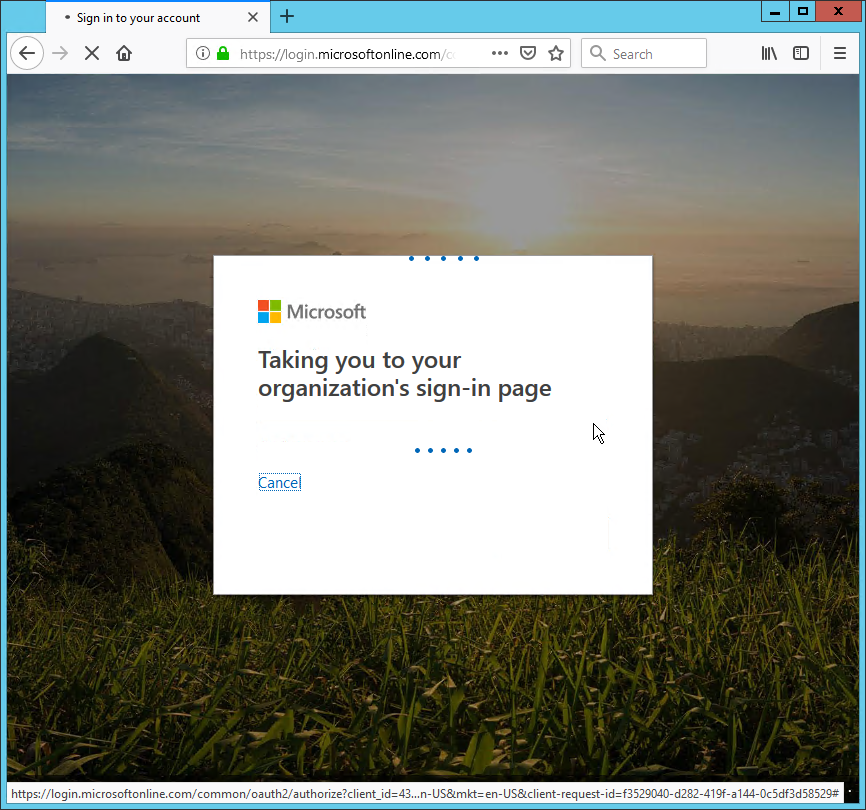
To test the Office 365 SSO Connection
...