Versions Compared
Key
- This line was added.
- This line was removed.
- Formatting was changed.
Before you connect EmpowerID to an external directory, there are a number of prerequisite steps you need to take. You only need to perform these steps the first time you connect to an external directory. These steps are as follows:
Setting the server role for each of your EmpowerID servers — Server roles determine what EmpowerID jobs (back-end processes) and Web services are enabled on a particular server. EmpowerID categorizes server roles in the following way:
All-in-One-Server — The server role runs all front-end Web services and back-end processes. This role is designed to be used if you have a small environment with only one EmpowerID server.
Application Server — This server role runs all back-end processes, known as Jobs in EmpowerID. By default it does not run any Web services.
Default — This server role has no Jobs or Web services associated with it. When you install EmpowerID on a server, EmpowerID assigns this role to the server. This is to ensure no Jobs or Web services run on a server not designated for those Jobs or Web services. You need to change this to the appropriate role for each EmpowerID server for that server to function as intended.
Web Front-End — This server role runs all Web services. By default it does not run any back-end processes.
Reviewing the Join and Provision Rules — When you connect EmpowerID to an external directory or other identity-aware application and turn on inventory, EmpowerID evaluates the accounts in those external systems to determine whether EmpowerID People should be provisioned from those accounts. The logic that determines this is specified by the Join and Provision Rules, as well as the filters in the Identity Warehouse. Thus, before turning on inventory, you should review these rules and filters and adjust them as needed.
| Expand | ||
|---|---|---|
| ||
Attribute Flow - Directory Change Processor Job — Job hosted by the Worker Role service that takes the attribute changes from the attribute inbox that were discovered during inventory and processes them using the attribute flow rules to update the Person object. Changes to the Person object can then lead to changes being pushed to the attribute outbox that will flow to other systems. This job is scheduled per AccountStoreaccount store. Account Lockout Detection Job — Job hosted by the Worker Role service that detects locked out user accounts. Account Password Reset Inbox — Job hosted by the Worker Role service that performs the offline password resets. Windows Service and AppPool Account Password Sync — Job hosted by the Worker Role service that synchronizes account password resets for accounts used by Windows Services and IIS App Pools. Attestation Policy Compiler — Synchronizes account password resets for accounts used by Windows Services and IIS App Pools. Attestation Processor — Not used - placeholder for customization. Database Archiving Rule Processor — Job hosted by the Worker Role service that performs database archiving rules and processes. Dynamic Hierarchy Generation Job — Job hosted by the Worker Role service that calculates which groups should be provisioned or deprovisioned in group hierarchy policies. Dynamic Hierarchy Membership Inbox Processor Job — Job hosted by the Worker Role service that syncs the group membership for each group in the grou hierarchy membership inbox. Dynamic Hierarchy Membership Recalculation Job — Job hosted by the Worker Role service that calculates which groups in group hierarchy policies should have their membership refreshed. Dynamic Hierarchy Provision Inbox Processor — Job hosted by the Worker Role service that calculates which groups should be provisioned or deprovisioned in group hierarchy policies. Group Membership Queue Processor Job — Job hosted by the Worker Role service that batch processes changes to group memberships. Group Membership Reconciliation Job — Job hosted by the Worker Role service that evaluates the current "as is" membership of groups versus the "should be" state of who should be a member based upon dynamic RBAC assignments of the "Member" Resource Role in EmpowerID. This job is scheduled per Resource System or Account Store. Inventory Job — Job hosted by the Worker Role service that claims inventory jobs for Resource Systems and Accounts stores on a scheduled basis and calls the inventory method for that system. For Account Stores, the inventory process is responsible for populating the attribute inbox and also it can run the initial Person provision process using the same Join and Provision Rule logic used by the Account Inbox One by One or Account Inbox Bulk permanent workflow. The actual implementation of how to inventory each system will be specific to the type of system and the implementation in its connector. This job is scheduled per Resource System or Account Store. Office 365 Batch Processor — Job hosted by the Worker Role service that performs the batch processing for Exchange Online Office365 actions. Permanent Workflow Job — Job hosted by the Worker Role service that ensure permanent EmpowerID workflows are kept in a continuously running state. Person Default Attributes Reinforcement Job — Job hosted by the Worker Role service that is responsible for making sure people have the mandatory attributes assigned by policy. It will also populate the outbox so accounts owned by the person are updated. RBAC Maintenance Job — Job hosted by the Worker Role service to calculate RBAC assignments. RBAC Security Compiler Job — Job hosted by the Worker Role service that is responsible for building the Location and Business Role trees. It also calculates the location of resource location and which security delegations will affect them. This job MUST run in only ONE server. RBAC Security Person Business Role Compiler Job — Job hosted by the Worker Role service that is responsible for calculating what business roles and locations a person will have based on all possible assignments. Resource Entitlement Inbox Processor Job — Job hosted by the Worker Role service that performs the actions specified by the Resource Entitlement Inbox entries (Provision, Deprovision, etc.). Resource Entitlement Recalculation Job — Job hosted by the Worker Role service that evaluates the current "as is" status of Resource Entitlement policies (RETs) versus the "should be" state. This entails determining what Accounts, Home Folders, Exchange Mailboxes, etc., people currently own versus what they should own by policy. The delta to normalize what they have with what they should have is written to the Resource Entitlement Inbox as a series of actions to be performed (Provision, Disable, Move, De-provision). Resource Role Reconciliation Job — Job hosted by the Worker Role service that manages the membership of EmpowerID Resource Role groups (RRGs). It determines who should currently be a member of those RRGs and then modifies the membership to match. This job is scheduled per Resource System or Account Store. Search Tag Compilation — Job hosted by the Worker Role service that evaluates and prepares the tags needed for tag searching in EmpowerID, it calculates implicit tagging. Rights Enforcement Job — Job hosted by the Worker Role service that adds or removes native permissions for resources in external systems based on the current state of RBAC delegations. The actual granting or revoking of rights for external systems can result in calls to other agents (e.g., the Exchange Agent) in order to complete the action. This job is scheduled per Resource System or Account Store. Rights Inventory Job — Job hosted by the Worker Role service that inventories native permissions for external system resources. The actual inventory of rights for the external system in question can result in calls to other agents (e.g., SharePoint Agent) in order to complete the action. Risk Factor and Stats Recalculation Job — Job hosted by the Worker Role service that is responsible for calculating the risk factor score for all EmpowerID actor types. Role and Location Compiler — Job hosted by the Worker Role service that is responsible for determining a person's roles and locations from external data. Role and Location Processor — Job hosted by the Worker Role service that is responsible for assigning roles and locations to a person, as determined by the compiler from external data. Separation Of Duties Policy Compiler — Job hosted by the Worker Role service that evaluates separation of duties policies to discover violations and creates Separation of Duties (SoD) Violation tasks. Separation Of Duties Violation Processor — Job hosted by the Worker Role service that performs default configured actions in response to SoD Violation tasks. Set Compiler Job — Job hosted by the Worker Role service that evaluates saved searches or Sets against connected Account Stores. The results of these compiled search can be used for query-based assignment of Person objects to Business Roles and Locations. |
| Expand | ||
|---|---|---|
| ||
Exchange Management Web Service — WCF web service hosted by Worker Role Windows Service that can execute any of the PowerShell cmdlets for managing Microsoft Exchange 2007 or greater. This service must be enabled on a machine loaded with the Exchange Management Console tools. LDAP Management Web Service — WCF web service hosted by IIS. This service must be enabled on a machine with connectivity to the LDAP directories that it manages. Lotus Notes Web Service — WCF web service hosted by IIS. This service must be enabled on a machine with Lotus Notes. Password Manager Web Service — WCF web service hosted by IIS specific for password management such as validation and also receives password change notification messages from the EmpowerID Password Change Detection Agent Window service. Pipeline Service Web Service — WCF web service hosted by IIS. This service must be enabled for BRE applications to function correctly and to receive system wide alerts and notifications. PowerShell Web Service — WCF web service hosted by IIS for executing any type of PowerShell cmdlets. This service will be used by workflows that execute PowerShell cmdlets. Applicable PowerShell snap-ins should be loaded on each server hosting this service. Service Bus Management Web Service — WCF web service hosted by IIS and provides a distributed WCF endpoint hosting facilities for integrating external resource systems and applications with the rest of the EmpowerID platform. The ESB Agent easily extends the life of existing legacy applications through the deployment of legacy application connectors developed in BPM Studio and deployed as WCF services on a ESB Agent. SharePoint Management Web Service — WCF web service hosted by IIS that can execute any of the SharePoint object model calls required for managing Microsoft SharePoint. Federation Server Web Service — WCF web service hosted by IIS. Provides a distributed Claim based STS for the EmpowerID platform. Windows Server Management Web Service — WCF web service hosted by IIS that can execute any of the local Windows server OS management actions required for shared folder creation or other system management tasks. This service must be enabled on a machine that is the intended target for management. Workflow Server Web Service — WCF web service hosted by IIS. Provides a secure service extension host to the workflow server. |
To configure the server roles for each of your EmpowerID servers
On the navbar, expand Infrastructure Admin > EmpowerID Servers and Settings and click EmpowerID Servers.
On the EmpowerID Servers page, click the EmpowerID Servers tab and search for the server whose role you want to configure.
Click the Edit button for that server.
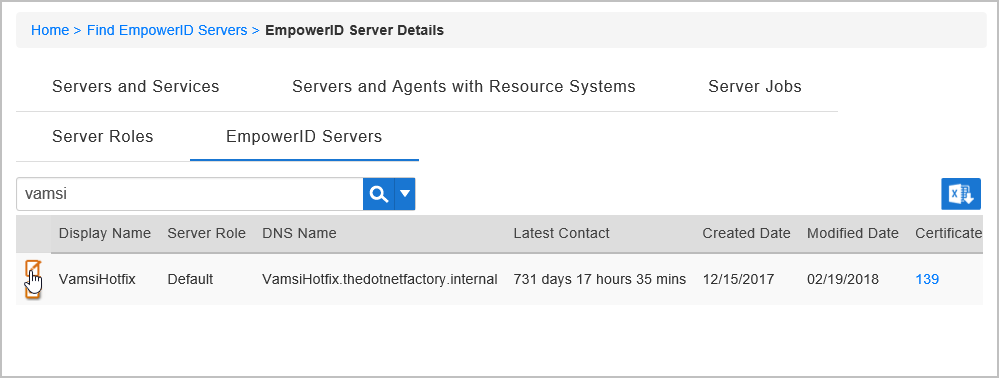 Image Removed
Image Removed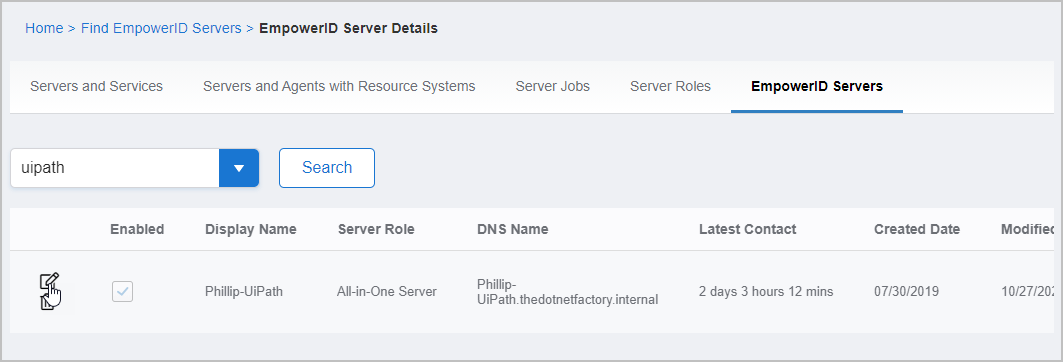 Image Added
Image AddedIn the dialog that appears, select the appropriate role from the EmpowerID Server Role drop-down.
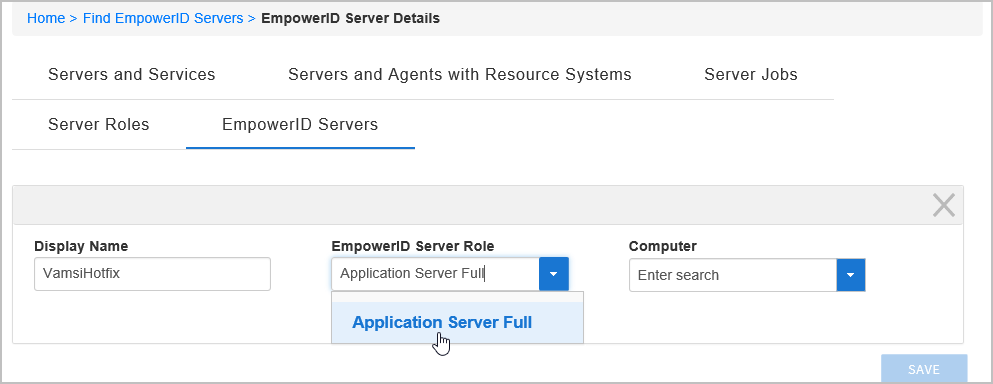 Image Removed
Image Removed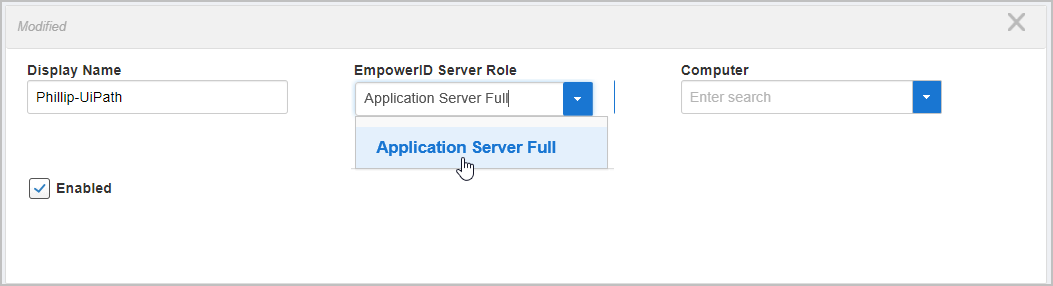 Image Added
Image AddedClick Save to save the role and close the dialog.
To review the Join and Provision rules for your environment
On the navbar, expand Infrastructure Admin> EmpowerID Servers and Settings and click EmpowerID System Settings.
Search for AccountInbox.
You should see a number of Account Inbox Join and Provision rules and filters, such as the AccountInboxJoinByBirthDateFirstNameLastName rule highlighted below.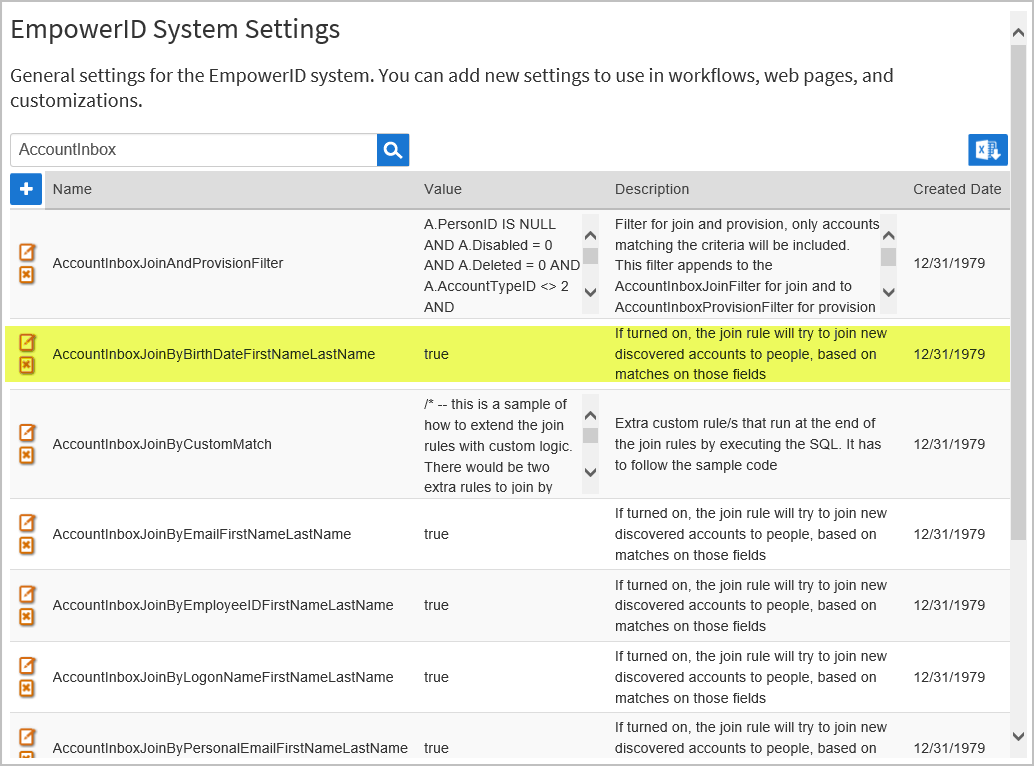 Image Removed
Image Removed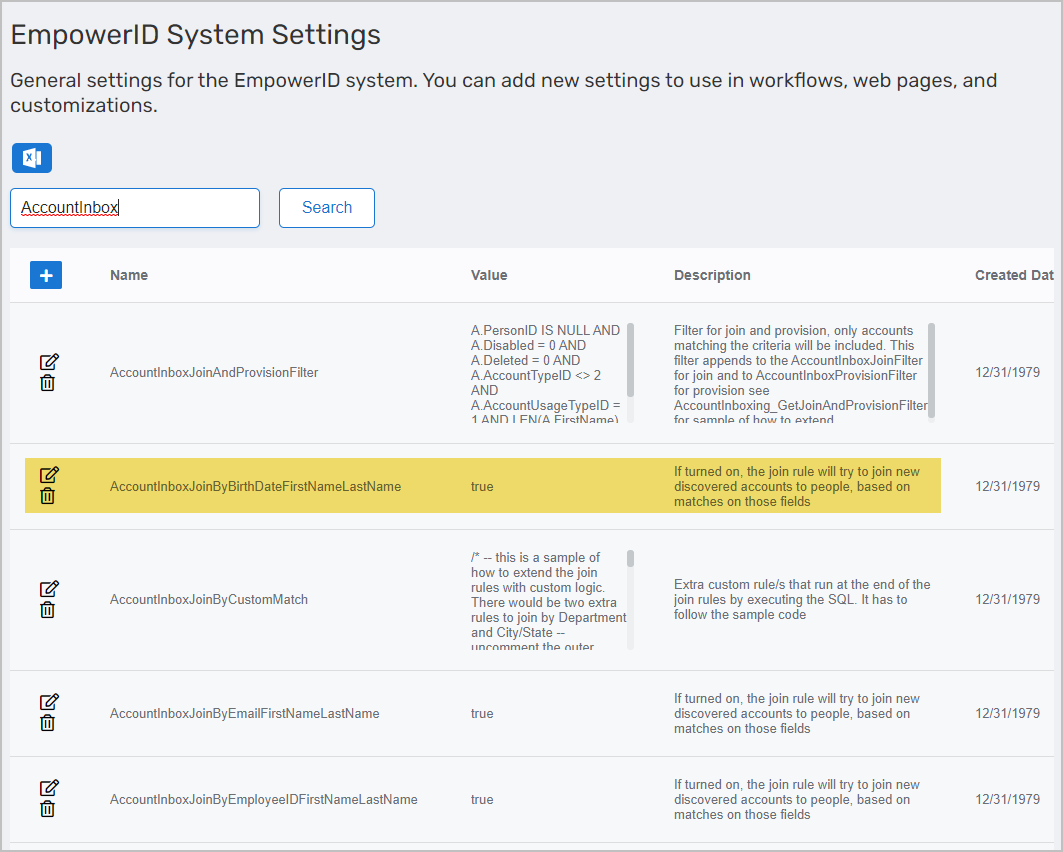 Image Added
Image Added
These Join rules work in conjunction with the Join and Provision filters to specify the conditions that must be met for EmpowerID to join newly discovered user accounts to an EmpowerID Person. The default logic of these Join Rules is to join an inventoried user account to an EmpowerID Person if the account store allows for Person joining and the applicable attributes on the user account match the corresponding attributes on an existing EmpowerID Person. For example, the above highlighted Join rule instructs EmpowerID to attempt to join newly discovered accounts to people if the Birth Date, First Name and Last Name attributes match.In addition to the above rule, EmpowerID includes the following Join Rules:
AccountInboxJoinByCustomMatch — This an empty rule that you can use to customize the attribute matches required to join an inventoried user account to an EmpowerID Person.
AccountInboxJoinByEmailFirstNameLastName — This rule instructs EmpowerID to attempt to join newly discovered accounts to people if the Email, First Name and Last Name attributes on a given user account match that of an existing EmpoweID Person.
AccountInboxJoinByEmployeeIDFirstNameLastName — This rule instructs EmpowerID to attempt to join newly discovered accounts to people if the EmployeeID, First Name and Last Name attributes on a given user account match that of an existing EmpoweID Person.
AccountInboxJoinByPersonalEmailFirstNameLastName — This rule instructs EmpowerID to attempt to join newly discovered accounts to people if the PersonalEmail, First Name and Last Name attributes on a given user account match that of an existing EmpoweID Person.
By default, each of the above Join rules are enabled (except for the Custom Join rule). You can disable any of these rules from the EmpowerID System Settings page by doing the following:
Locate the rule you want to disable and click the Edit button for that rule.
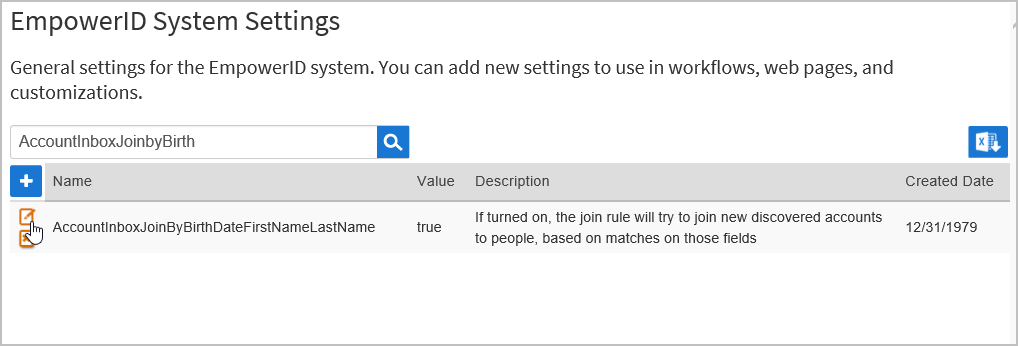 Image Removed
Image Removed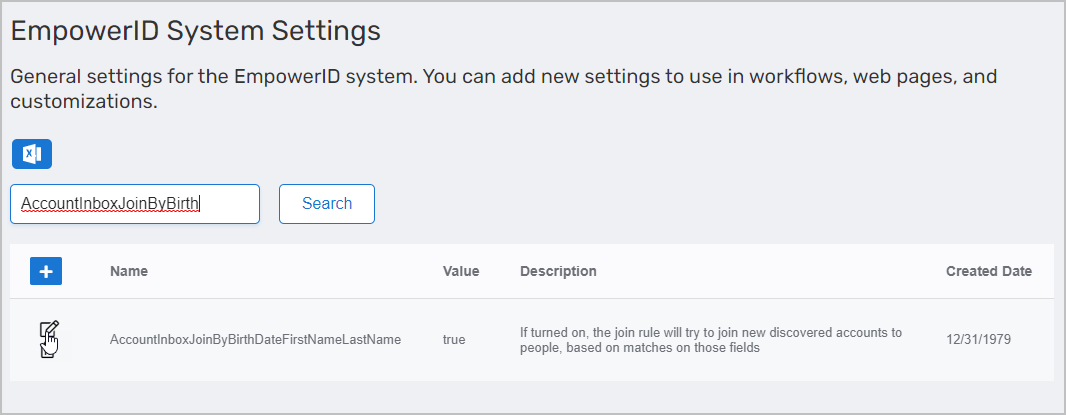 Image Added
Image AddedIn the Value field of the dialog that appears, replace true with false and click Save.
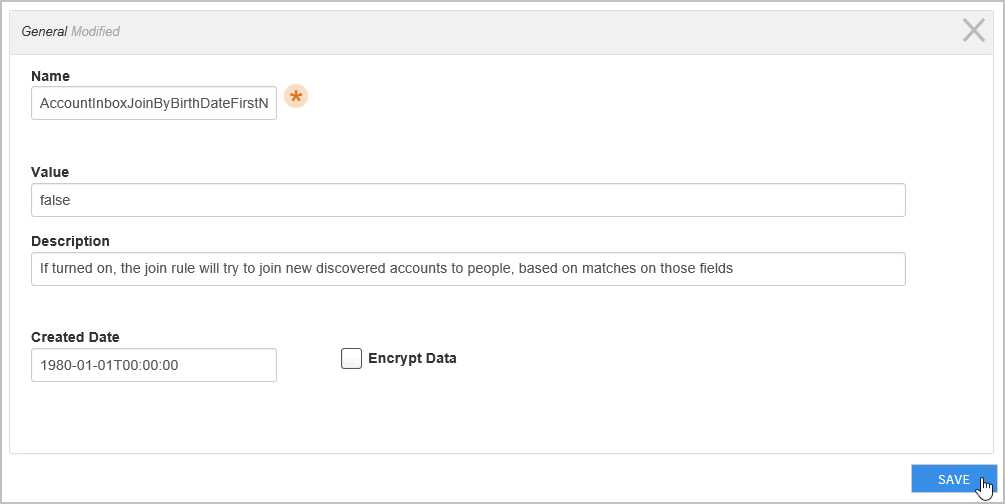 Image Removed
Image Removed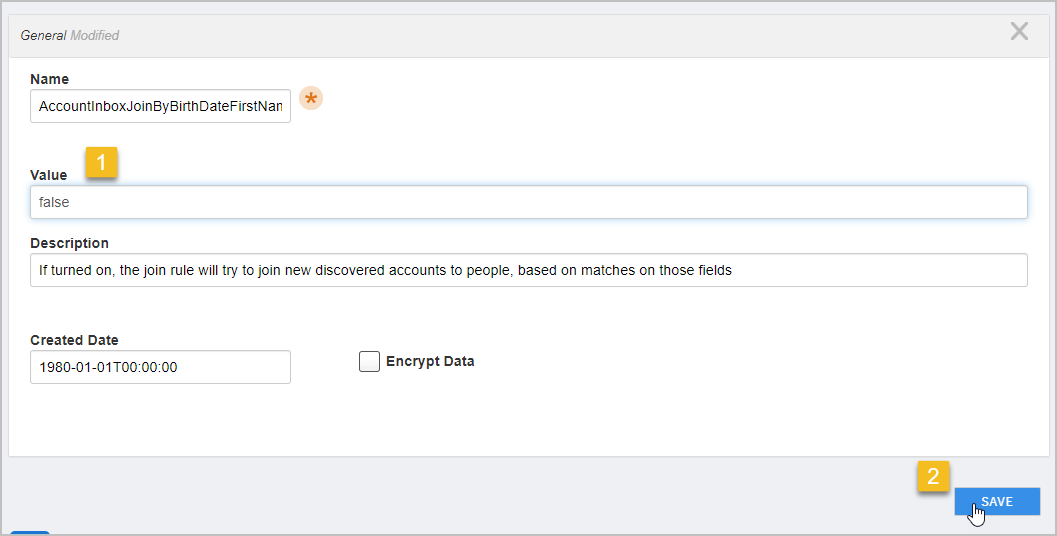 Image Added
Image Added
To review the Join and Provision filters for your environment
On the navbar, expand Infrastructure Admin > EmpowerID Servers and Settings and click EmpowerID System Settings.
Search for AccountInbox.
Select the filter you want to edit and click the Edit button for that filter.
In the Value field of the dialog that appears, add any additional logic to the filter and then click Save.
In our example, we edit the JoinAndProvisionFilter to specify that in addition to the default conditions, user accounts must also have an Employee Type of Permanent.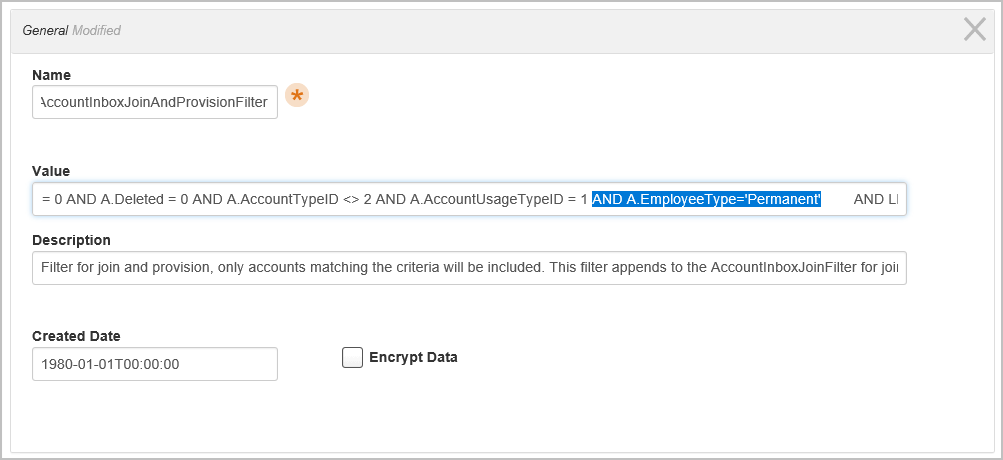 Image Removed
Image Removed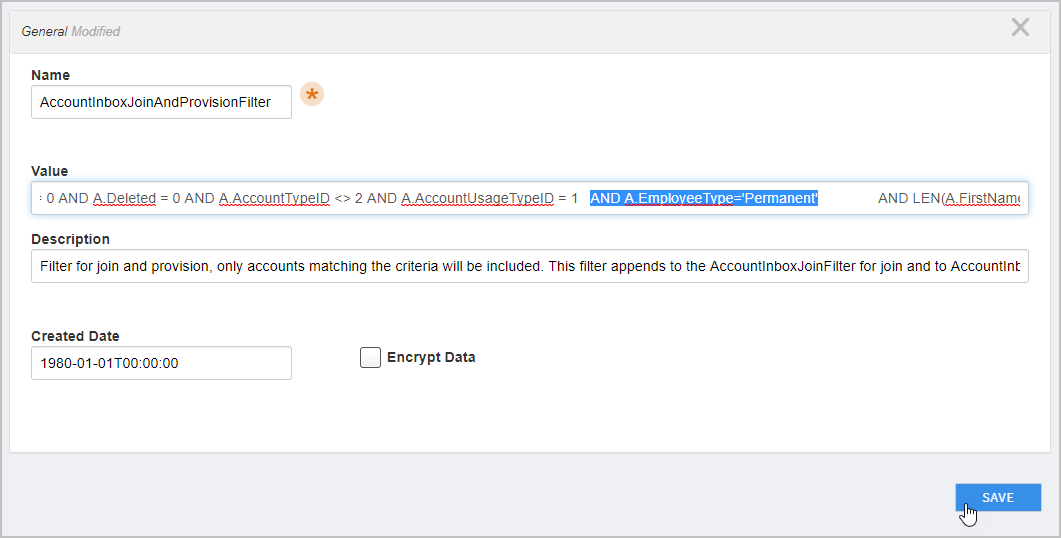 Image Added
Image Added
| Warning |
|---|
As the AccountJoinAndProvision filter is used to target which account are eligible for both joining and provisioning, the filter should only be customized in situations where the custom criteria applies to accounts that are both join and provision targets. |
| Insert excerpt | ||||||
|---|---|---|---|---|---|---|
|
| Expand | ||
|---|---|---|
| ||
CONCEPTS Overview of the EmpowerID Identity Warehouse Projection and Enforcement Overview TASKS |
| Div | ||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| ||||||||||||||||
IN THIS ARTICLE
|