IBM AS/400 (IBM i)
Before connecting EmpowerID to an external directory, please review the Getting Started with Directory Systems topic. The topic walks you through the prerequisites you need to complete before connecting to an external directory for the first time. These prerequisites include:
- Configuring the appropriate server roles for your EmpowerID servers
- Reviewing the Join and Provision Rules for your environment
- Reviewing the Join and Provision Filters for your environment
If you have already connected EmpowerID to another external directory, you can skip these prerequisites.
Once IdentityForge has been configured for EmpowerID, you can add an AS/400 Identity Forge Connector domain to the EmpowerID Identity Warehouse as a managed Account Store. This topic demonstrates how to do so.
Prerequisites
Before connecting EmpowerID to AS/400, you must configure Identity Forge for EmpowerID. See IdentityForge for details.
To create an account store for IBM i using the web application
- In the Navigation Sidebar, expand Admin, then Applications and Directories, and click Account Stores and Systems.
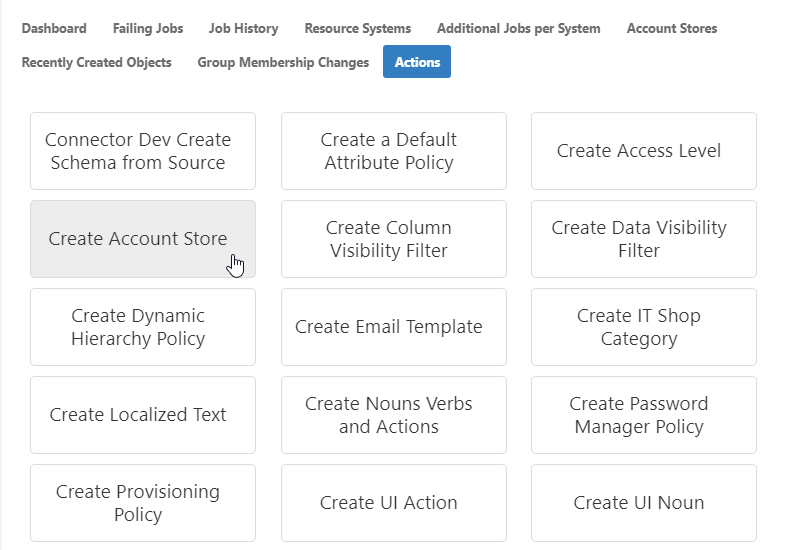
- Click the Actions tab, and then click the Create Account Store action.
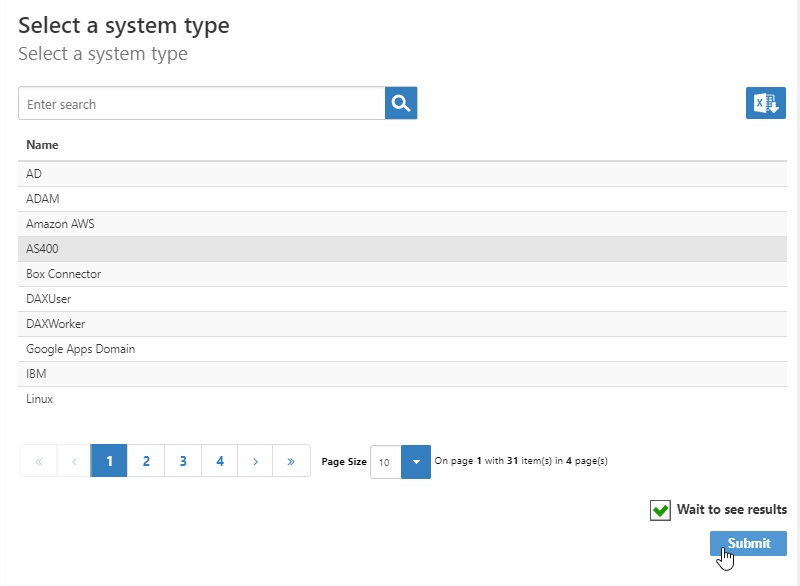
- Select AS400 from the list of Security Boundary types and click Submit.
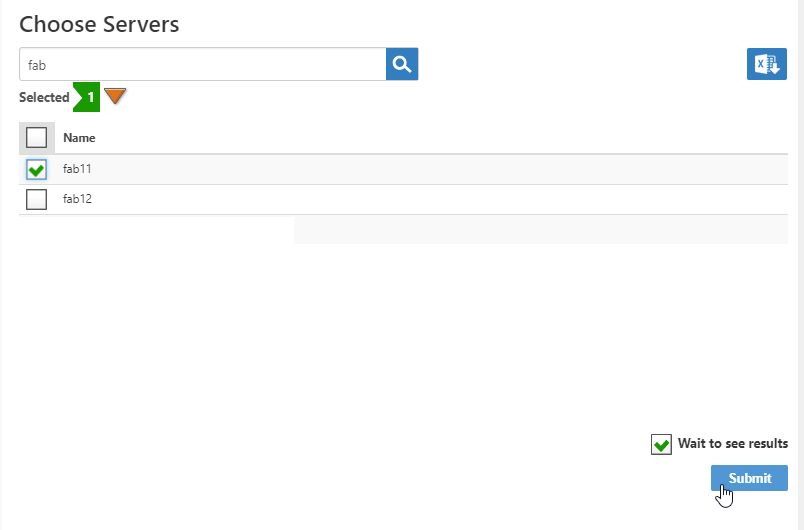
In the Choose Servers page that appears, select one or more EmpowerID servers and click Submit.
The Choose Servers page displays only those servers where the EmpowerID Web Role service is running. If you do not see your server on the page:
- Ensure that the server has either the All-in-One Server or Web Front-End server role.
- Ensure that the EmpowerID Web Role service is running.
All selected servers must be in the same forest and able to communicate with the AS/400 Directory over LDAP port TCP 389.
On the IBM i (AS400) Settings page that appears, enter settings to connect to your AS400 environment to allow EmpowerID to discover and connect to it.
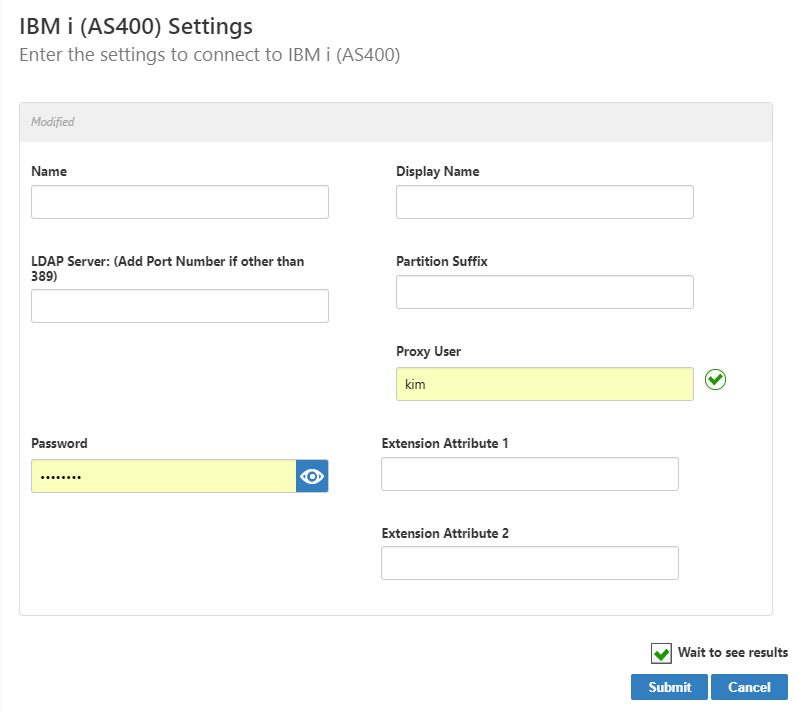
- In the Name and Display Name fields, enter a name for the account store.
- LDAP Server — The name of the server on which the directory is installed. Include the port number if it is other than 389, e.g. dc01.eiddoc.com:636.
- Partition Suffix — The suffix of the partition in which the data resides, e.g. dc=as400,dc=com.
- Proxy User — The user account must have read access to the partition that holds the objects in the directory. You can change this at any time.
- Password — The proxy account password. These credentials are saved as the default proxy connection credentials for the AS400.
- Extension Attribute 1 — These fields are for any additional information required, such as default library and library list or default SQL schema.
- Extension Attribute 2 — These fields are for any additional information required, such as default library and library list or default SQL schema.
- Click Submit.
- The Account Store and associated Resource System are created and appear in both the web application and in the Management Console.
To edit account store settings on the web
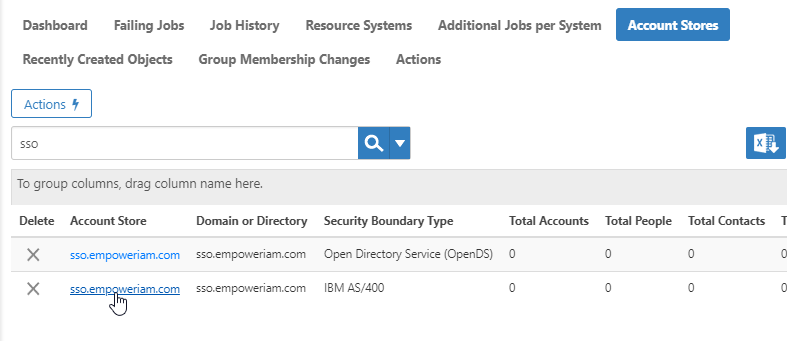
- In the Navigation Sidebar, expand Admin, then Applications and Directories, and click Account Stores and Systems.
- On the Account Stores tab, search for the account store you just created and click the link to go to its details page.
- On the Account Store Details page, click the Edit button or the name of the account store.
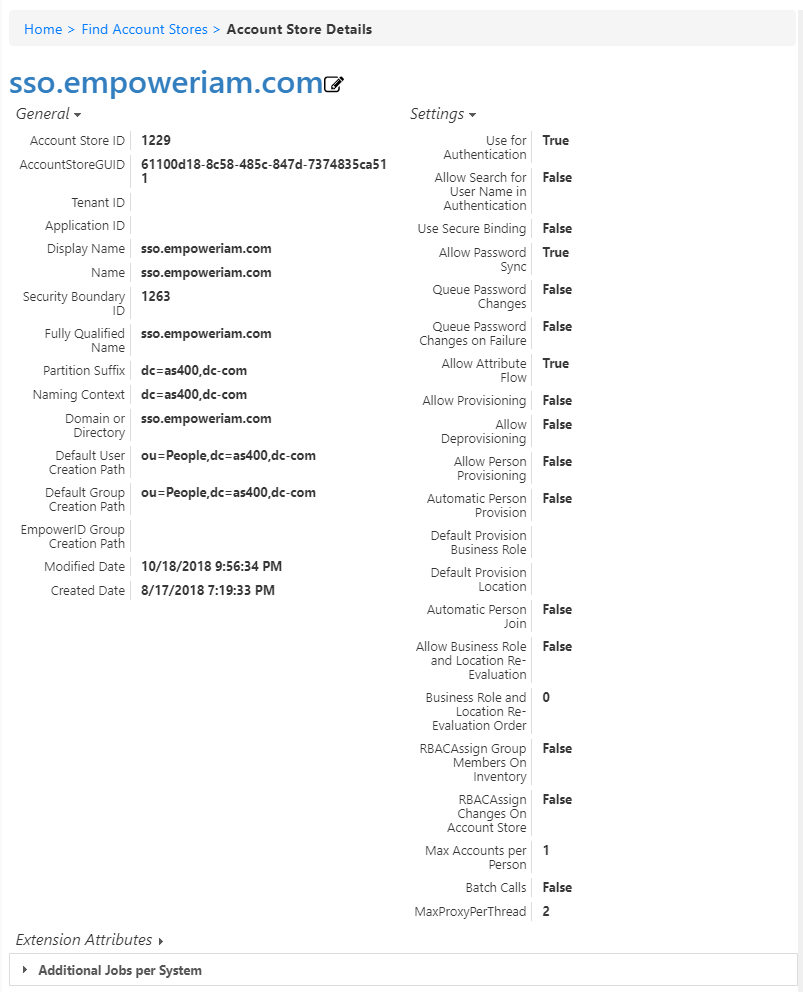
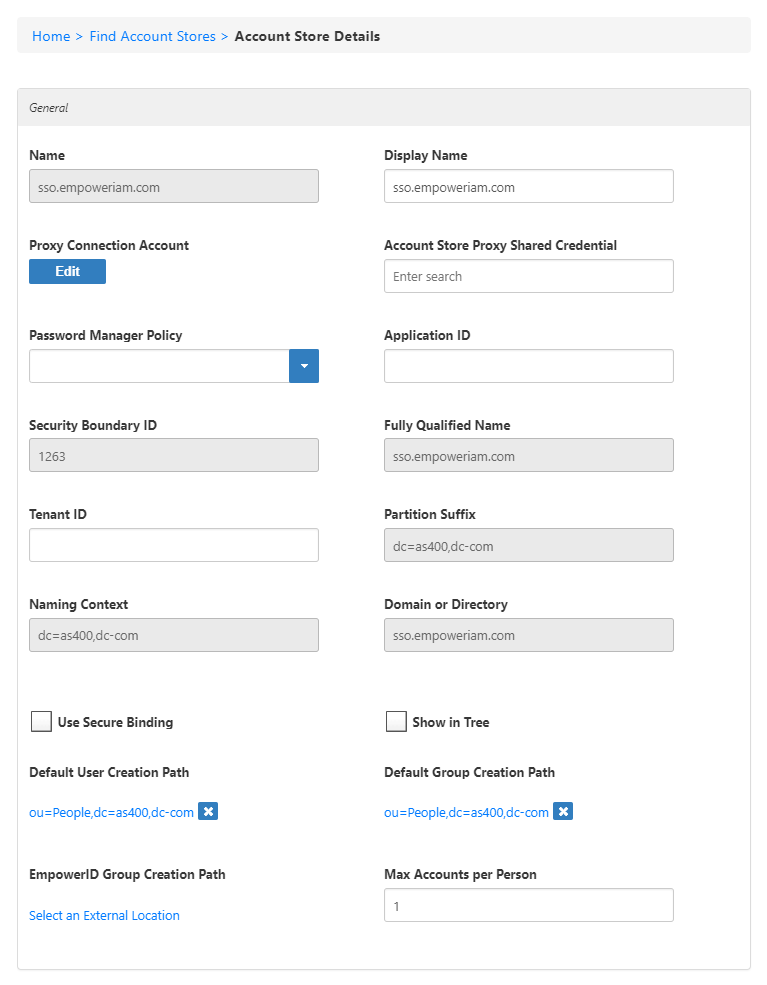
- In the edit view of the page, you can edit values in any of the enabled fields. In the General section, these are:
- Display Name — Edit the name of the account store as it appears in the list of account stores.
- Proxy Connection Account — Change the instance, user name, and password for the connection.
- Account Store Proxy Shared Credential — Click in this box and press Enter to see a list of shared credentials in your system to use for the proxy connection.
- Password Manager Policy — Select a password manager policy to use for the account. If not selected, it uses the Default Password Manager Policy.
- Application ID — If the account store is a one-to-one match with a Tracking Only application, enter the Application Resource GUID of the application. (This value is supplied automatically if you select the Create a New Account Directory option when creating a Tracking Only application.)
- Tenant ID — Enter the Tenant ID, if supplied by the connection account. (AWS uses this.)
- Use Secure Binding — Toggle to bind accounts with encryption.
- Show in Tree — Toggle to show the account store in the Locations tree.
- Default User Creation Path — Select a location in which to create users if none is specified.
- Default Group Creation Path — Select a location in which to create groups if none is specified.
- EmpowerID Group Creation Path — Select a location in which to create EmpowerID groups if none is specified.
- Max Accounts per Person — Enter the maximum number of user accounts from this domain that an EmpowerID Person can have linked to them. This prevents the possibility of a runaway error caused by a wrongly configured Join rule. We recommended setting this value to 1 unless users commonly have multiple accounts and you want them to be joined to the same person.
- In the Features section, you can select any of these values:
- Use for Authentication — Toggle to allow users to log into EmpowerID using domain authentication. Use the domain\username format or enable Allow Search for User Name in Authentication.
- Allow Search for User Name in Authentication — Toggle to allow users to log in without specifying a domain name. When enabled, EmpowerID first checks to see if the user name entered exists within its Identity Warehouse and if so attempts to authenticate as that user. If a matching logon name exists but the login fails, EmpowerID then searches through all account stores where Allow Search is enabled to find the correct user name and password combination.
- Allow Password Sync — Toggle to allow EmpowerID to sync password changes discovered during inventory.
- Queue Password Changes — Toggle to have EmpowerID send password changes to the Account Password Reset Inbox for batch processing.
- Queue Password Changes on Failure — Toggle to have EmpowerID send password changes to the Account Password Reset Inbox only when the change fails.
- Allow Account Creation on Membership Request — Toggle to allow users without accounts to request group membership and automatically have an account created.
- Batch Calls —
- Allow Attribute Flow — Toggle to allow attribute changes to flow between EmpowerID and the account store.
- Allow Person Provisioning — Toggle to allow EmpowerID to create Person objects from the user records discovered during inventory.
- Allow Provisioning — Toggle to allow EmpowerID to create new Groups in ServiceNow from requests discovered during inventory.
- Allow Deprovisioning — Toggle to allow EmpowerID to delete Groups in ServiceNow based on requests discovered during inventory.
- Automatic Person Join — Toggle to allow EmpowerID to join newly discovered accounts to people during the inventory process if they meet the Join Rule as specified by the Custom_Account_InventoryInboxJoinBulk SQL stored procedure.
- Automatic Person Provision — Toggle to allow EmpowerID to provision EmpowerID people for new accounts discovered during the inventory process if they meet the Provision Rule specified by theCustom_Account_InventoryInboxGetAccountsToProvision SQL stored procedure.
- Default Provision Business Role — Set a default Business Role to assign people if none is specified.
- Default Provision Location — Set a default Location to assign people if none is specified.
- Allow Business Role and Location Re-Evaluation — Toggle if you have multiple account stores to manage and want to specify a priority for each.
- Business Role and Location Re-Evaluation Order — Enter a number to specify the priority of the account store for determining the Business Roles and Locations to assign to a Person. Account Stores with a higher value take precedence.
- Recertify All Group Changes — Toggle to allow EmpowerID to generate recertification review tasks for all changes in ServiceNow Groups.
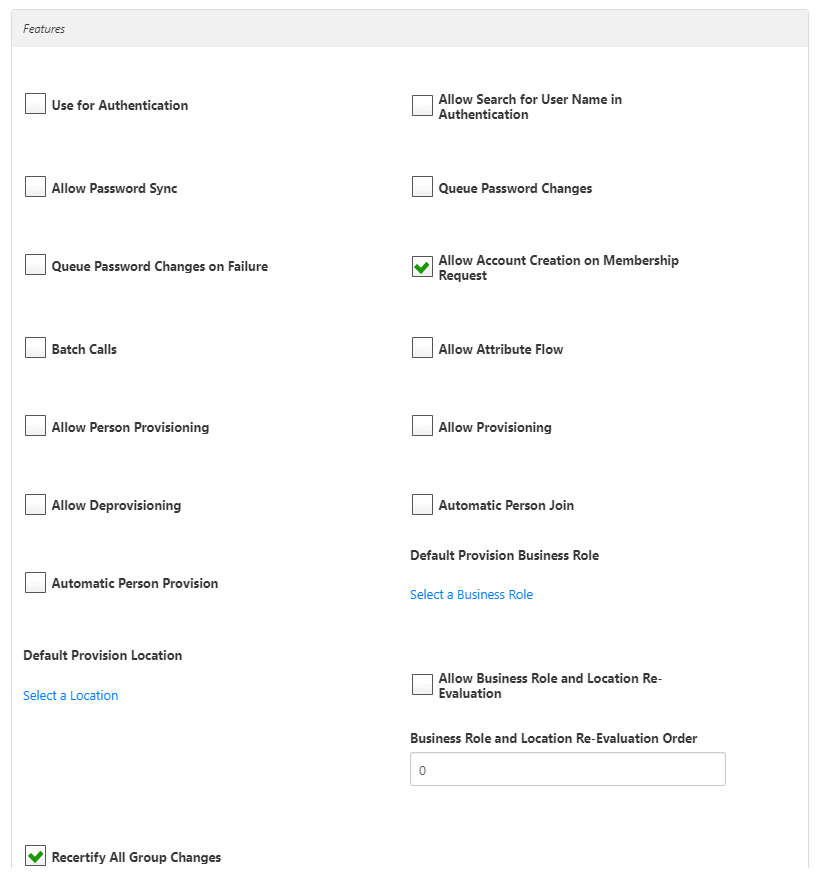
- When you have finished editing, click Save.
To connect to IBM i (AS/400) using the Management Console
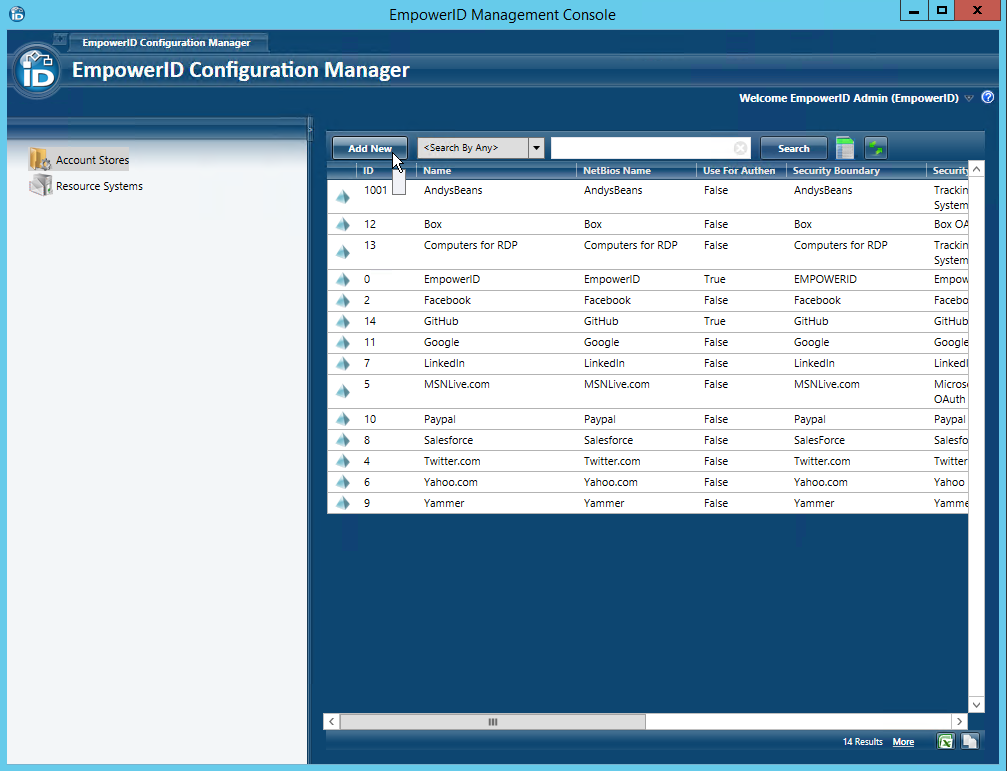
- Log in to the EmpowerID Management Console as an administrator.
- Click the application icon and select Configuration Manager from the menu.
- In Configuration Manager, select the Account Stores node and then click the Add New button above the grid.
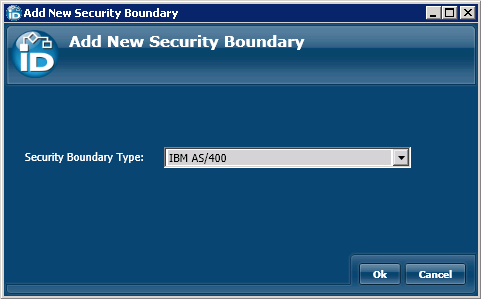
- In the Add New Security Boundary window that opens, select the IBM AS/400 Security Boundary type from the drop-down list and then click OK.
This opens the AS400 Directory window.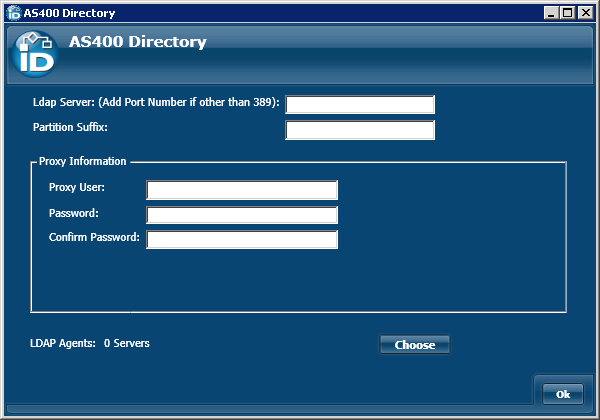
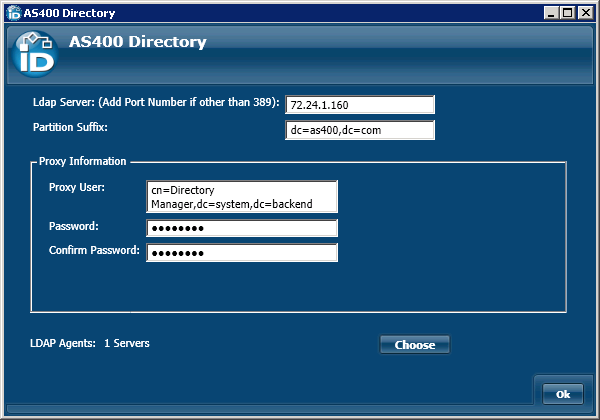
- In the AS400 Directory window, do the following:
- Enter the name of the server on which the directory is installed and include the port number if it is other than 389 in to the Ldap Server field.
- Enter the partition suffix in the Partition Suffix field.
- Enter the proxy information into the fields of the Proxy Information panel. The user account must have read access to the partition that holds the objects in the directory. The user account entered here is saved as the default proxy account (connection credential) used when managing these objects. You can change this at any time.
At this point, the AS400 Directory window should look similar to the following image.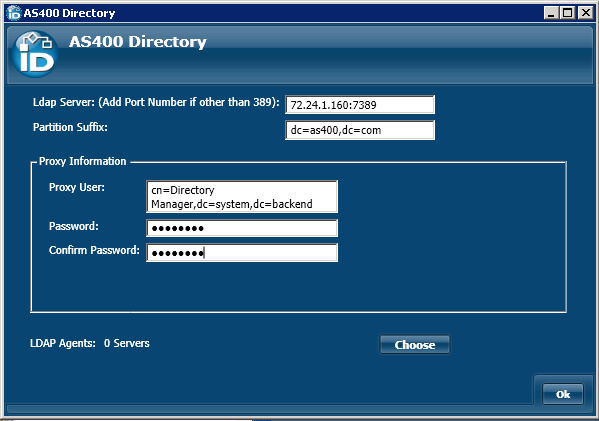
- Click the the Choose button below the Proxy Information panel to open the Choose Servers window. This window provides the interface for selecting the server(s) where the EmpowerID AS/400 Agent(s) reside.
- In the Choose Servers window that appears, toggle the Server button from a red sphere to a green check box for each server running the EmpowerID AS/400 Agent. You must pick a server running the Agent that is in the same Forest and can communicate with the AS/400 Directory over LDAP port TCP 389. Please note that the agent must be started on a server before the server will show in the Choose Servers window.
- Click OK to close the Choose Servers window.
- This returns you to the AS400 Directory window, which should look similar to the following image.
- Click OK to close the AS400 Directory window.
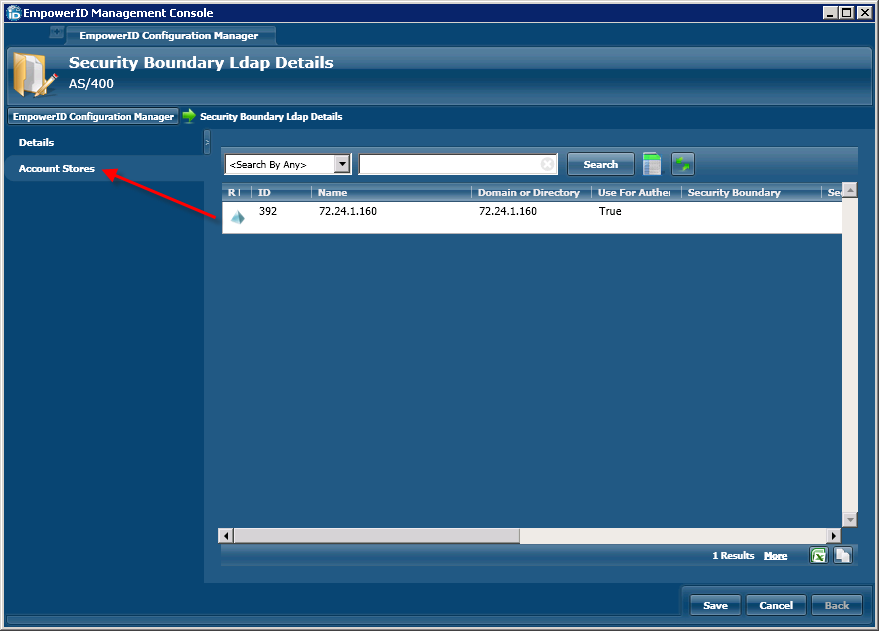
- In the Security Boundary Ldap Details screen that appears, change the Display Name from the server and port to something more friendly, such as AS/400. You should see the new display name appear on the screen.
- Click the Account Stores tab to the left of the screen.
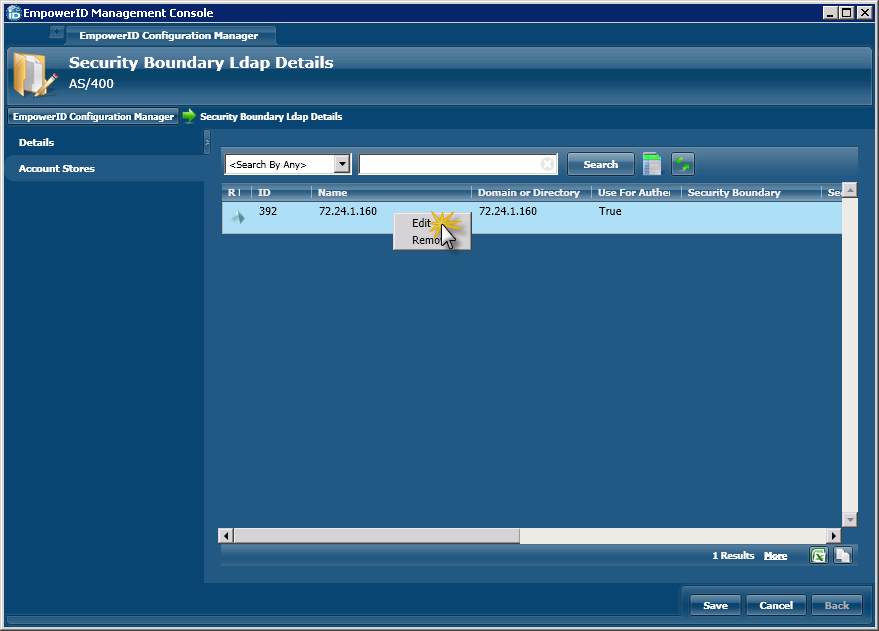
From the grid to the right of the tab, double-click the AS/400 Security Boundary or right-click it and select Edit from the context menu.
This opens the Account Store Ldap Details screen. This screen is used to configure the settings that EmpowerID uses to manage the domain. A description of the settings available from this screen follows.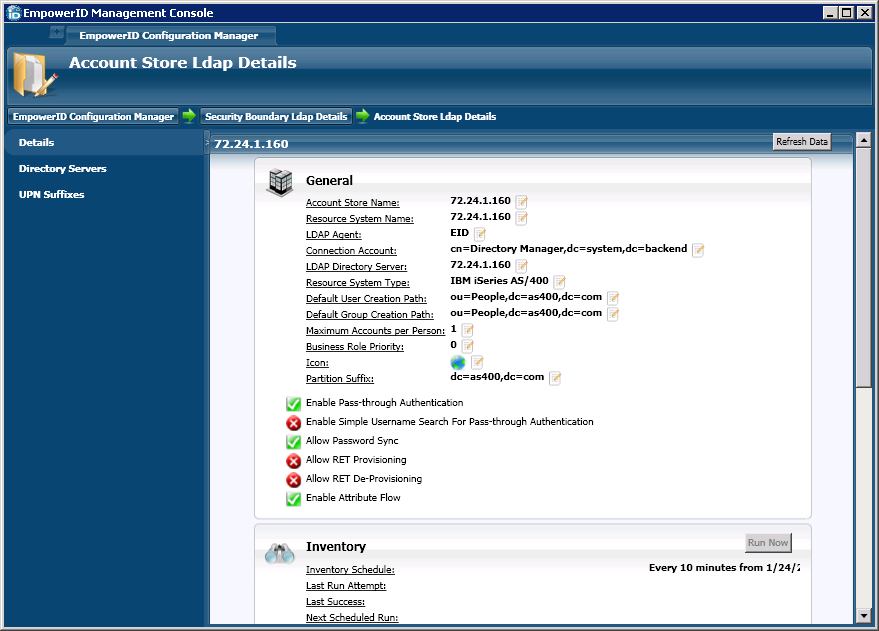
Once you have completed the configuration of your Account Store, you should:
- Configure the attribute flow rules for the account store (by default all attributes except the mail attribute are set for bidirectional flow).
- Map your external locations to corresponding EmpowerID Locations.
- Turn on inventory.