Granting permanent elevated privileges to your admins represents an open security vulnerability. You can avoid this by using vaulted admin credentials in EmpowerID so that usernames and passwords are stored in a secure, encrypted password vault. When your system admins require elevated privileges for use in a PowerShell script, the EmpowerID system retrieves the credentials and generates a PSCredential object for them to use.
This topic shows how non-admins can retrieve shared admin credentials from EmpowerID for use in your PowerShell scripts.
Create a shared credential in EmpowerID. For more information, see Vaulting Non-Computer Credentials. |
To create an OAuth client application (one time setup)
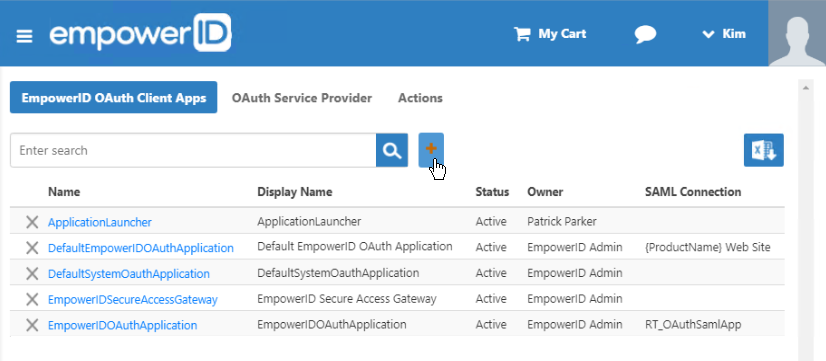
- In the navigation sidebar, expand Admin, then SSO Connections, and click OAuth.
- In the EmpowerID OAuth Client Apps tab of the OAuth page, click the Add button above the grid.
In the OAuth Provider Application Details page that appears, enter information in the fields about the application for which you want to share credentials to use in your PowerShell script.
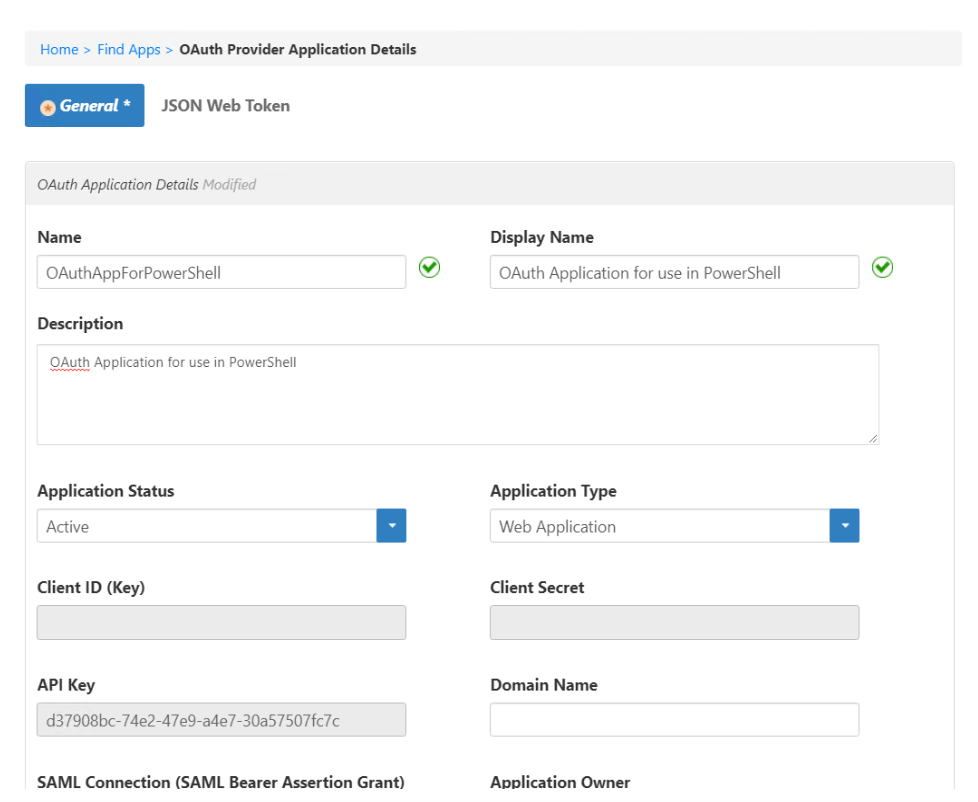
For more information on OAuth applications, see Creating an OAuth Application for Andy's Beans.
- Scroll to the bottom and click Save. When it finishes, click the Find Apps link in the breadcrumbs to return to the list of OAuth Client Apps.

- Find your app in the list and click the Name value to open the OAuth Provider Application Details page.
- The Connection Details section contains the values that you can copy for use in the PowerShell script:
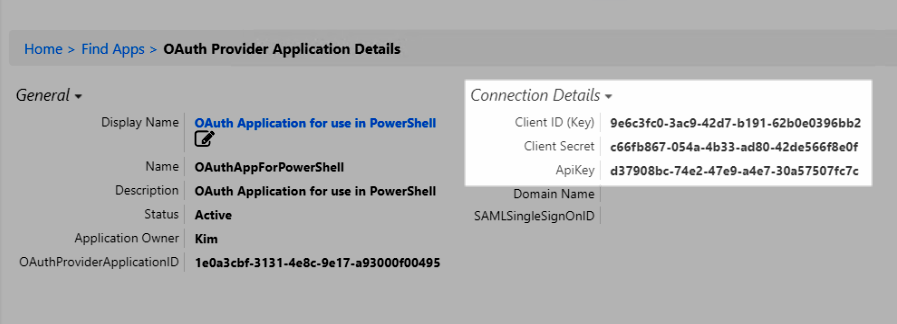
- Client ID (Key) – copy this value to use for the $ClientID
- Client Secret – copy this value to use for the $ClientSecret
- API Key – copy this value to use for the $APIKey
To create a PowerShell script to retrieve the credentials
In Windows PowerShell ISE (or any text editor), paste the following script:
Replace the following values in the script:
$ClientID – replace the xxx with the GUID value from the Client ID (Key) of your OAuth application
$ClientSecret – replace the xxx with the GUID value from the Client Secret of your OAuth application
$APIKey – replace the xxx with the GUID value from the API Key of your OAuth application
- $RedirectURL – replace sso.empoweriam.com with the FQDN of your server
- $TokenURL – replace sso.empoweriam.com with the FQDN of your server
- $CheckoutURL – replace sso.empoweriam.com with the FQDN of your server
- $GetCredentialURL – replace sso.empoweriam.com with the FQDN of your server
- $SearchURL – replace sso.empoweriam.com with the FQDN of your server
- Save the file as GetCredentials.ps1.
To run the PowerShell file
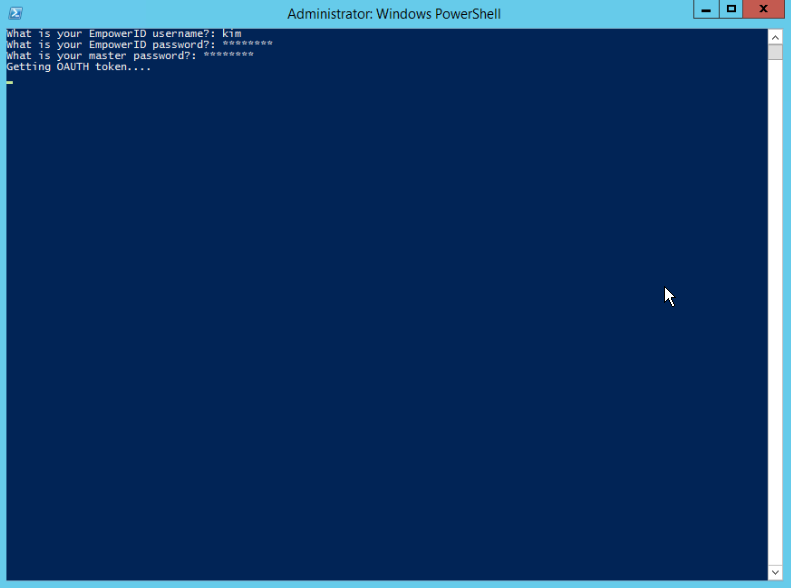
- In File Explorer, right-click the saved file and select Run with PowerShell.
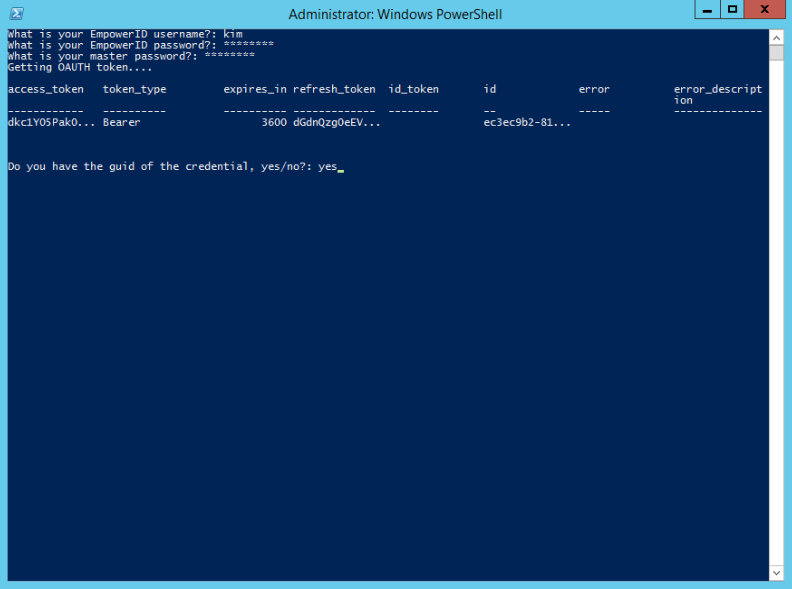
- PowerShell opens and prompts you for several values. Answer each and press Enter. The script retrieves the OAuth token.
- Once the token is retrieved, you are asked whether you have the GUID of the credential. If you respond yes, you must provide the GUID, otherwise, you are prompted to search for the credential. Here we respond yes.
- To copy the GUID for the credential:
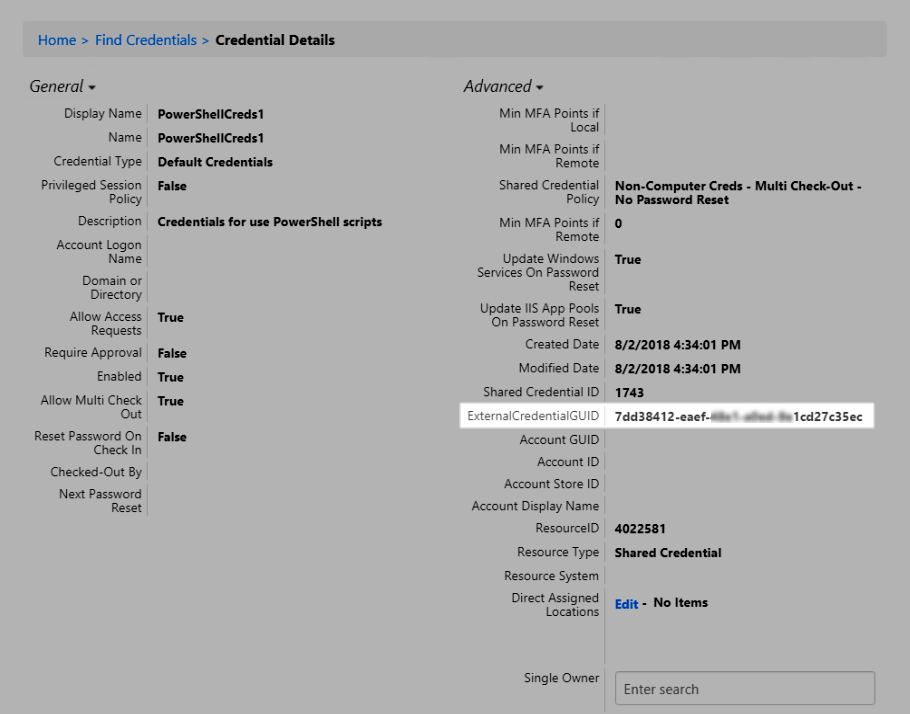
- In the Navigation Sidebar, expand Privileged Access and click Shared Credentials.
- Click the Credentials I Manage tab, and then click the display name of the credential we created above.
- In the Credential Details page, expand the Advanced section and copy the ExternalCredentialGUID value.
Paste this value at the PowerShell prompt and press Enter. PowerShell proceeds to check out the credentials.
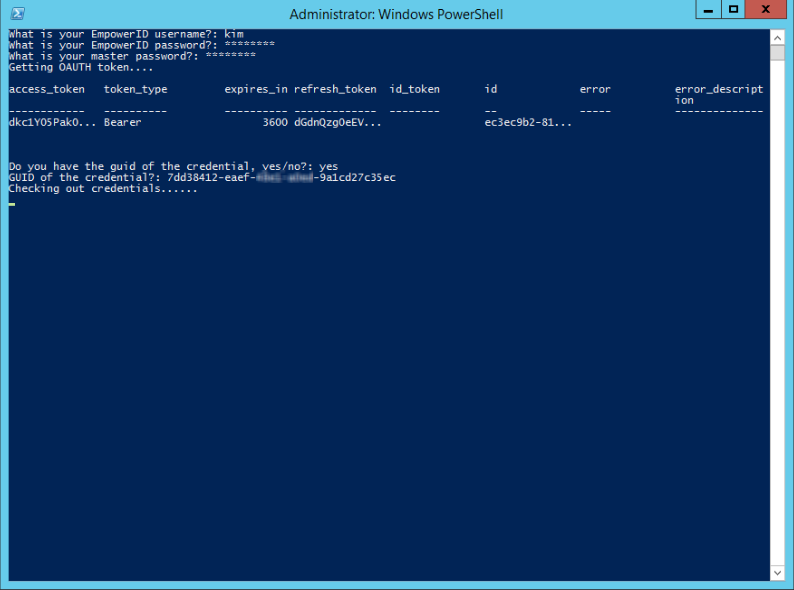
If your PowerShell instance disappears instead of checking out the credentials, your server may not be set to allow you to execute scripts.
See About Execution Policies in the Microsoft PowerShell documentation to learn how to change your execution policy.
- The retrieved credentials are stored in a global variable: $credentialsfromREST.
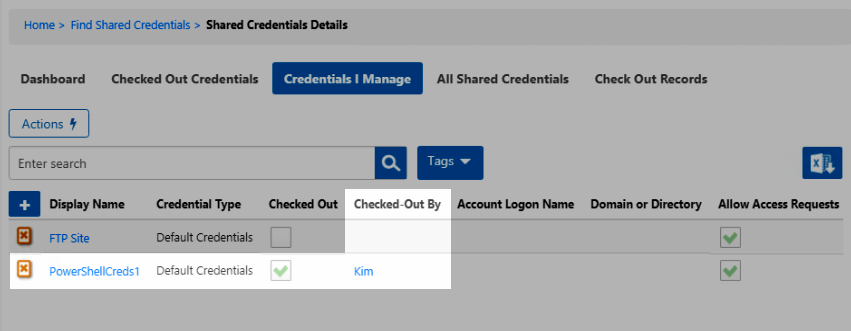
- In EmpowerID, you can verify that the credentials are checked out on the Shared Credentials page, Credentials I Manage tab.
|
|